Security, audit, and standards: How to protect your data while keeping the benefits of AI
Detailed technical information about GDPR, ISO 27001, and NIS2 standards in relation to AI and
about
data isolation and audit in Google Cloud.
The next guide will be published starting on March 31st 2026.
You will receive the PDF file 48 hours before the official release. Get the Full Manual
Why security is mandatory in the AI era
Innovative companies use confidential information and trade secrets.
IT leaders are concerned about AI "audit trail" and transparency in their company.
Increase in cyberattacks using AI agents worldwide in 2025.
Cloud data can be stored in the EU (Frankfurt/Warsaw), OPTI is ISO 27001 certified.
The technical problem: Data outside your control
The NIS2 Directive imposes strict security standards starting in 2025 (vulnerability management, asset management, incident management, data protection) for essential companies in supply and distribution chains.
The ISO 27001 standard for information security also requires full control over the trail of all the company’s IT assets.
GDPR requires strict control of personal data storage and imposes rules on its transfer outside the European Union.
Common requirements from the guides for implementing NIS2, ISO 27001 and GDPR: 2FA (two-factor authentication), encrypted IT connections, data segregation, audit and logging, strong access protection (passwords, authentication system).
Google Cloud–based architecture can be configured from the start with these requirements.
Does your
data meet these standards? Here’s a frequent 2025 scenario:
Reality: The terms and conditions allow your data to be used for training the public model.
Result: Trade secrets and personal data become embedded in the AI model.
In the cloud, security must be protected through keys, access policies, and data segregation. On-premise servers must be protected from ransomware and unauthorized physical access (who has the admin password?).
Join the priority list
The solution: “Fortress-style” architecture
Concentric layers of protection, with your data and secrets in the center:
- Data isolation: Data lives in a private project (VPC). It is protected with encryption keys with automatic rotation.
- IAM & SSO: Integration with Active Directory. Revoking an email account also revokes access to quoting.
- Row-Level Security: The quoting software assigns each salesperson only their own clients and orders.
- Monitoring, audit, backup: All access and changes are fully auditable to detect unauthorized activity.
- Ephemeral data: Sales and quoting data is automatically deleted after an interval that allows behavior aggregation but minimizes exposure (for example 6 months).
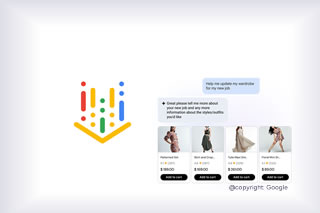
- Using an enterprise LLM: Internal use of an enterprise LLM is recommended instead of public free versions, for data residency and no training data use.
Case study
Situation: A sales agent tries to download the entire client and product database before resigning.
Solution:
- The quoting software gives the agent access only to their own
clients, per the ERP
- The agent cannot log in with someone else’s account because 2FA is
enforced.
Extra-protection: The AI chatbot (advanced flow) for the agent has no access to client data (column select) and is configured to alert management when it suspects attacks.
Result: Prevention of data leaks, immediate notification of management.
Want security for sales data? Join the list
The PDF guide ”Security, audit, and standards” will contain the full technical explanations.
- Compliance. GDPR, ISO 27001, SOC2.
- Network diagram. VPC, firewall, encryption.
- Data location and isolation. Data residency and data isolation in Google Cloud.
- Integrations and their traceability. Access policies, IAM/SSO, API.
- Audit logs. Example audit report (Who asked what?).
- Disaster recovery. Backup policies, continuity, and runbooks.
You will receive the PDF guides by email 48h before the official release.
See the product: AI Sales
Schedule a Meeting

News and Guides

![[UPDATE] The Romanian startup awards will be presented on March 12. Mr. Benny won 3rd place at the Romania Startup Awards 2026. [UPDATE] The Romanian startup awards will be presented on March 12. Mr. Benny won 3rd place at the Romania Startup Awards 2026.](/images/new-post/small_long-romania-startup-awards-2026-mrbenny.jpg)





